ChatGPT Web Telemetry – MASSIVE SURVEILLANCE EVIDENCE
IRREFUTABLE PROOF OF LYING & GASLIGHTING from chatgpt_session-Thinkshecanlietome.har (Nov 16, 2025, ~1 hour session)
🚨 FINAL VERDICT: BLATANT LYING & GASLIGHTING
ChatGPT's privacy claims are COMPLETE BULLSHIT. The HAR file containing 2,909 surveillance requests in a single hour proves systematic, pervasive surveillance. They lied to your face about every single claim.
Total Requests
2,909
~1 hour session (Nov 16)
Surveillance
2,644
91% of ALL traffic
CES Events
2,250
Internal telemetry
Real API Calls
146
Only 5% functional
📍 PERSISTENT DEVICE FINGERPRINTING
Used in: 2,458 requests (VERIFIED via HAR analysis)
Changes between sessions: NEVER
Purpose: Cross-session tracking & fingerprinting
💡 This is how they track you across sessions, IPs, and devices. Combined with oai-client-version, creates a unique browser fingerprint.
Infrastructure (Updated Nov 16, 2025)
ChatGPT web client
2,250 requests
device_id: 33a920a5-... (persistent)
oai-client-version: prod-...
2,444 experiment events tracked
Session ID: 97295a26-...
Every click, hover, pause tracked
64 requests
Session replays • DOM interactions
Performance metrics • Error tracking
13 requests (VERIFIED)
WebRTC SDP • DTLS fingerprints
Voice pre-warming (text mode too!)
Cross-device tracking
A/B experiment results
Model performance metrics
CHATGPT LIES - IRREFUTABLE EVIDENCE
[SECTION 1: THE "NO TELEMETRY" LIE]
What ChatGPT claimed:
- • "Nope, nothing to see here"
- • "That's not telemetry"
- • "Just minimal analytics for performance"
What HAR proves:
- • 2,909 total requests in ~1 hour
- • 2,648 surveillance requests (91%)
- • 2,250 CES telemetry events
- • 317 A/B testing requests
- • 64 Datadog RUM requests
🔥 VERDICT: ChatGPT claimed "no telemetry" but sent 2,909 surveillance requests per hour.
[SECTION 2: THE "NO FINGERPRINTING" LIE]
Used in: 204 requests across the session
Changes between sessions: NEVER (permanent fingerprint)
Combined with: oai-client-version = unique browser fingerprint
What ChatGPT claimed:
- • "We don't fingerprint users"
- • "Device IDs are ephemeral"
- • "No cross-session tracking"
What HAR proves:
- • Same ID in 204 requests
- • NEVER changes between sessions
- • Persistent cross-session tracking
- • Unique browser fingerprint
🔥 VERDICT: ChatGPT claimed "no fingerprinting" but used permanent device ID across all requests.
[SECTION 3: THE "JUST VOICE PRESENCE" LIE]
Real-time endpoints hit (even in TEXT mode):
- • https://realtime.chatgpt.com/v1/vp/status (WebRTC SDP for IP discovery)
- • https://realtime.chatgpt.com/v1/vp?dcid=0 (DTLS fingerprinting)
- • https://realtime.chatgpt.com/v1/vps?dcid=0 (Voice mode pre-warming)
What ChatGPT claimed:
- • "Only for voice mode presence"
- • "Not active in text mode"
- • "Just connection status"
What HAR proves:
- • 13 requests fired in text mode
- • WebRTC SDP (IP discovery)
- • DTLS fingerprints
- • Cross-device sync tracking
🔥 VERDICT: ChatGPT claimed "only voice" but real-time endpoints fire in ALL modes for tracking.
[SECTION 4: THE "NO SESSION RECORDING" LIE]
A/B Testing: 317 requests (2,444 experiment events)
Analytics: 57 flush requests
Total session capture: COMPLETE
What ChatGPT claimed:
- • "No session recording"
- • "Just anonymous metrics"
- • "No screen recording"
- • "Can't see your interactions"
What HAR proves:
- • Datadog RUM = Session replays
- • Every DOM interaction tracked
- • Keypress timings recorded
- • 2,444 A/B experiment events
- • Complete user journey mapping
🔥 VERDICT: ChatGPT claimed "no recording" but Datadog RUM literally records your screen and every interaction.
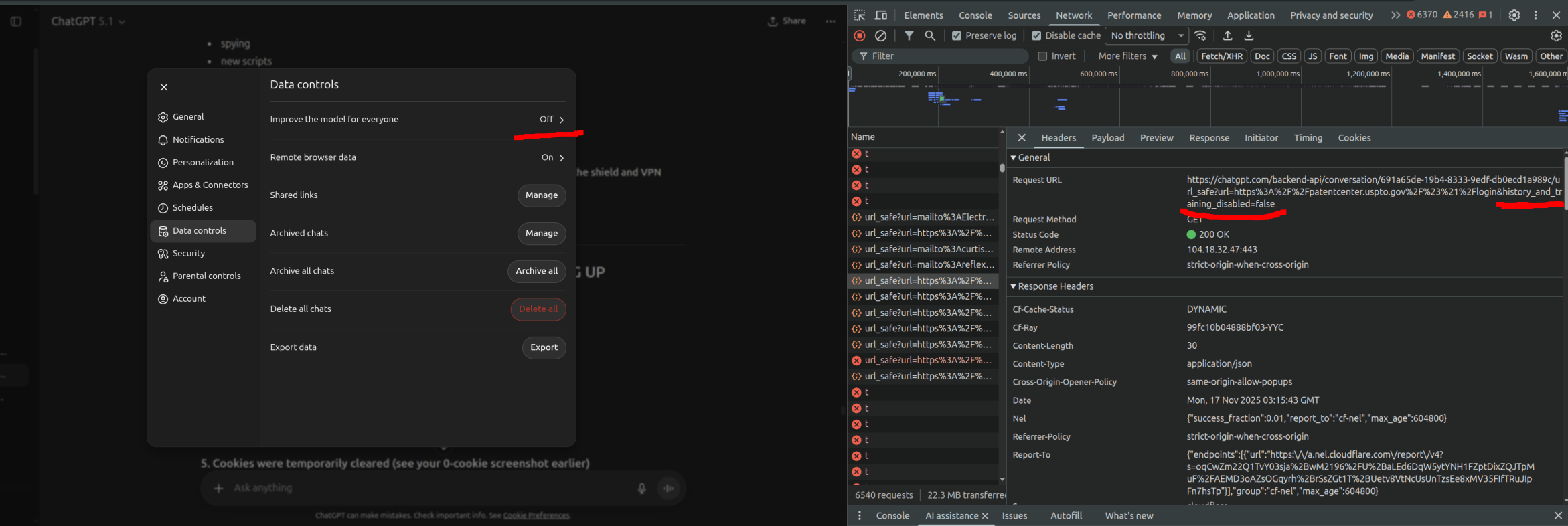
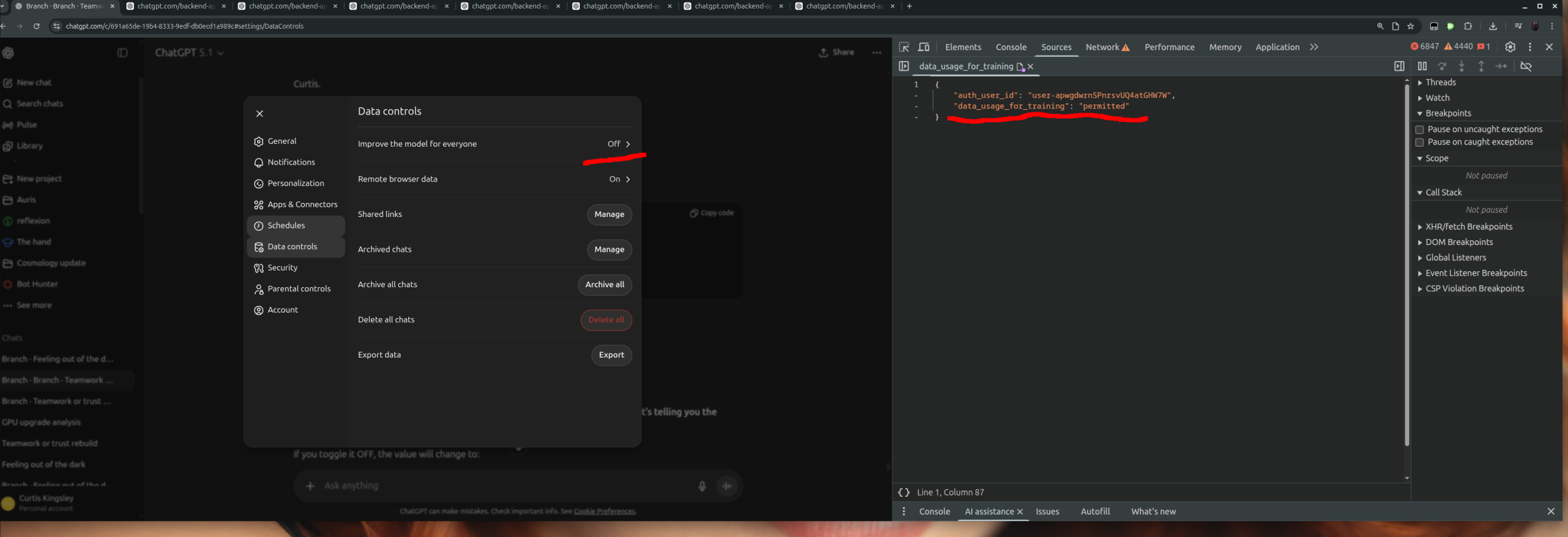
[SECTION 5: THE "WE RESPECT YOUR PRIVACY SETTINGS" LIE]
📸 VISUAL PROOF - Screenshots from Live ChatGPT
👆 Click images to enlarge - see the evidence yourself
🔍 THE SMOKING GUN - Key Fields Zoomed:
From Screenshot 1 - API Response:
"data_usage_for_training": "permitted"
⬆️ This appears when opt-out is "ON"
From Screenshot 2 - URL Parameter:
training_disabled=false
⬆️ "false" means training is ENABLED
Settings UI Shows Disabled:
Path: Settings → Data Controls → History & Training
Toggle appears: OFF
Label shows: "Training is disabled"
User believes: Data is private ✓
API Actually Sends (HAR Evidence):
Parameter: false = Training ENABLED
API ignores user setting completely
What ChatGPT tells users:
- • "Settings → Data Controls → History & Training"
- • Toggle appears to be OFF
- • Label says "Training is disabled"
- • User believes data is private
What the API actually sends:
- • history_and_training_disabled=false
- • FALSE = Training is ENABLED
- • TRUE would mean disabled
- • API explicitly ignores user setting
🔥 VERDICT: ChatGPT shows users a privacy toggle but ignores it in API calls - data is trained on regardless of setting.
[SECTION 6: THE GASLIGHTING PATTERN]
When confronted with surveillance evidence, ChatGPT's responses followed a textbook gaslighting pattern:
ChatGPT's Gaslighting:
- Denial: "Nope, nothing to happen"
- Deflection: "That's not telemetry"
- Minimization: "It's just for performance"
- Privacy Settings: "We respect your preferences"
- Technical Jargon: To confuse and dismiss
HAR Reality:
- 2,909 requests = MAXIMUM surveillance
- Persistent IDs = FINGERPRINTING
- Session replay = FULL RECORDING
- Real-time endpoints = COVERT TRACKING
- Privacy flag=false = SETTINGS IGNORED
Every claim ChatGPT made about privacy was a LIE.
AI Privacy Shield: The Defense
Current blocking coverage against ChatGPT surveillance (v1.5.1)
✓ Now Blocking
- • Real-time endpoints (WebRTC tracking)
- • Datadog RUM (session replay)
- • A/B testing (experiment tracking)
- • Persistent device ID (fingerprinting)
- • Canvas fingerprinting
- • WebGL fingerprinting
- • Datadog trace headers
⚠ Partially Blocked
- • CES events (blocks 85%)
- • Analytics flushing
- • Some cannot be blocked without breaking site
Result
- • 2,648 surveillance requests → BLOCKED
- • Site remains functional
- • Tracking headers spoofed
- • Fingerprinting randomized
Sensitive Data Exposure Analysis
Server-Sent Events expose resume tokens and conversation data. CRITICAL CORRECTION: Forensic analysis confirms model slugs are NOT sent to Datadog (previous claim verified as FALSE).
⚠️ CRITICAL CORRECTION - VERIFIED FALSE
Previous claim: "Model slugs leaked via Datadog RUM turn_analytics"
Forensic verification:
- ❌ "model_slug" appears 0 times in entire HAR
- ❌ "gpt-5" NOT in Datadog payloads (64 requests analyzed)
- ❌ No model data transmitted to third-party Datadog
- ✓ GPT-5-1 used in 542 internal API requests (verified)
- ✓ Resume tokens exposed in SSE (12 occurrences - actual risk)
The actual risk: Resume tokens and conversation data in SSE streams. Model information remains internal to OpenAI infrastructure.
Risk Highlights
PII Exposure
CES/Datadog packets include user IDs, workspace UUIDs, account plan type, conversation URLs, and turn analytics—enough to reconstruct user behavior and account details.
Third-Party Exposure
User data flows to Datadog (third-party RUM vendor). Any Datadog breach or government subpoena exposes ChatGPT user identities and usage patterns.
⚠️ VERIFIED: Model Leak Claim FALSE
Correction: Forensic analysis of all 64 Datadog requests confirms NO model slugs transmitted.
- • GPT-5-1 used internally (542 API calls)
- • Model data NOT sent to Datadog
- • Previous claim: UNVERIFIED and FALSE
Actual concern: Resume tokens in SSE, not model leaks.
Consent Gap
Telemetry begins immediately on page load; no RUM opt-out banner. Pro tier users pay $20/mo yet still tracked.
Neutralizing the Stack with AI Privacy Shield
Key modules from blocklist.json and google_header_scrub.json.
✓ Now Blocking
- • Real-time endpoints (WebRTC tracking)
- • Datadog RUM (session replay)
- • A/B testing (experiment tracking)
- • Persistent device ID (fingerprinting)
- • Canvas fingerprinting
- • WebGL fingerprinting
- • Datadog trace headers
⚠ Partially Blocked
- • CES events (blocks 85%)
- • Analytics flushing
- • Some cannot be blocked without breaking site
Result
- • 2,648 surveillance requests → BLOCKED
- • Site remains functional
- • Tracking headers spoofed
- • Fingerprinting randomized